Work with vCO over SSL
With the increasing popularity of VMware vCenter Orchestrator, there is a growing desire to use it over SSL connections. While vCO supports this type of connectivity out of the box, it is not necessarily pre-configured automatically to have a proper SSL certificate. Regardless of how or where you import the default certificate, you are unlikely to get away from warnings such as:
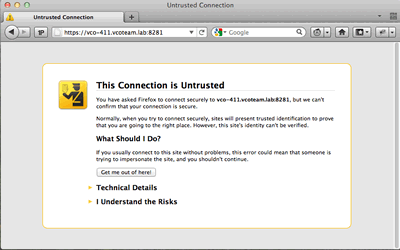
Firefox Warning:
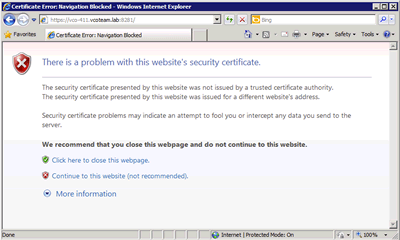
Internet Explorer Warning:
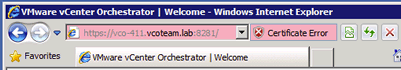
After clicking "Continue to this website (not recommended). ", you still get the "Certificate Error" red notification in the address bar -
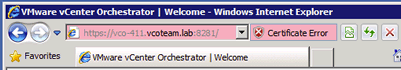
even if you import the certificate as a trusted store! While you are able to continue working via a web browser, a third party system accessing the API over HTTPS may not be as cooperative!
The purpose of this tutorial is to give you step-by-step guidance on resolving the issue above by creating a certificate that matches your vCO's server name.
The following steps require the use of the keytool program found in your JRE install. Don't worry about getting it because if you're reading this, then you must have vCO installed and the file is already on your server!! Here are some important paths for you to be aware of:
Keytool: <vCO install folder>\jre\bin\keytool.exe
jssecacerts file: <vCO install folder>\jre\lib\security\jssecacerts
The following commands will directly modify the existing keystore file without the need to change any configuration files. Before proceeding, please be sure to create a backup copy of your jssecacerts file.
- Stop your vCO Server Service
- Open a command prompt as administrator (Use the start menu to find command prompt, then right click and choose to 'run as administrator')
- Delete the current "dunes" key from the keystore using the following command:
keytool -delete -alias dunes -keystore "c:\program files\vmware\orchestrator\jre\lib\security\jssecacerts" -storepass "dunesdunes"
vRO 6 Virtual Appliancekeytool -delete -alias dunes -keystore "/etc/vco/app-server/security/jssecacerts" -storepass "dunesdunes"
- Generate a new certificate for the "dunes" key (10 year cert shown in sample line below - adjust validity in days as desired)
keytool -genkey -keyalg RSA -alias dunes -keystore "c:\program files\vmware\orchestrator\jre\lib\security\jssecacerts" -storepass "dunesdunes" -validity 3650
vRO 6 Virtual Appliancekeytool -genkey -alias dunes -keypass "dunesdunes" -keystore "/etc/vco/app-server/security/jssecacerts" -storepass "dunesdunes" -validity 3650
- When prompted for your first and last name, enter the FQDN of your vCO server. This is very important as it will tie the certificate to the server! For my example here, I will enter vco-411.vcoteam.lab (my test server in my test domain):
What is your first and last name? [Unknown]: vco-411.vcoteam.lab
- For each of the remaining prompts (Organizational Unit, Organization, City, State, Country Code), simply enter the appropriate values for your organizaiton
- After specifying the information above, you will be prompted for confirmation... Type "yes" and hit <ENTER>
- When prompted for the password for <dunes> hit <ENTER> to use the same as the keystore password (dunesdunes).
- Go back to your vCenter Orchestrator Configuration and Start the vCenter Orchestrator Server service via the "Startup Options" tab.
As an example:
With Internet Explorer (IE):
- Open your browser to https://yourvCOServer.domain.ext:8281/
- When prompted, click "Continue to this website (not recommended)."
- Now IE should have the "Certificate Error" listed to the right of your address bar - left click there and choose "View Certificates"
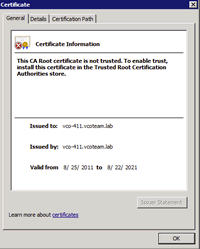
NOTE: you may need to have the vCO server added as a trusted site in order to get the "Install Certificate" button to be visible. In the following screenshots, the left image is before the vCO server is trusted and the right is after it is trusted:
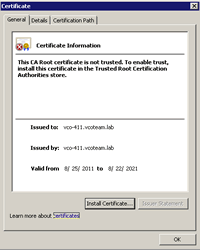
- Click the Install Certificate button
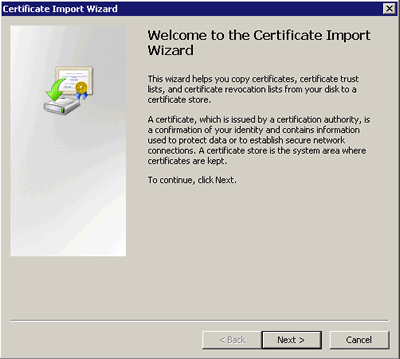
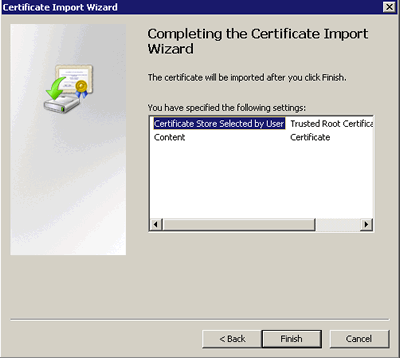
- The "Certificate Import Wizard" will launch - click "Next":
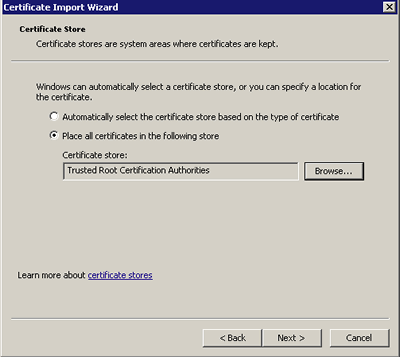
- On the next screen, choose to "Place all certificates in the following datastore, then browse and choose "Trusted Root Certification Authorities" and click "Next"
- On the final screen, click "Finish"
- Now, close IE and then re-open it and visit the vCO server over SSL. You should no longer be prompted with warnings or have a Certificate Error to the right of the address bar
At this point, other applications and systems (such as VMware Service Manager) should be able to successfully connect to the vCO SOAP API over SSL with no trouble!
OPTIONAL - Get CA Signed Cert
To generate CSR:
keytool -certreq -alias dunes -keypass "dunesdunes" -keystore "c:\Program Files\VMware\Orchestrator\jre\lib\security\jssecacerts" -storepass "dunesdunes" -file myCertRequest.csr
Send "myCertRequest.csr" to CA, you may need to convert the certificate you receive to DER if this is not the default, then import the response in the following way:
keytool -importcert -alias dunes -keypass "dunedunes" -file vcoCertificate.crt -keystore "c:\Program Files\VMware\Orchestrator\jre\lib\security\jssecacerts" -storepass "dunesdunes"
When using a CA issued cert, you may also be required to import the CA cert, and any intermediate CA certs, into the vCO server. These may be imported using the SSL tab under the vCO Configuration interface.

